Use Case
Security control hardening
The Challenge
60% of security incidents will be traced to misconfigured security controls
Identify and address security gaps and misconfigurations before they are exploited
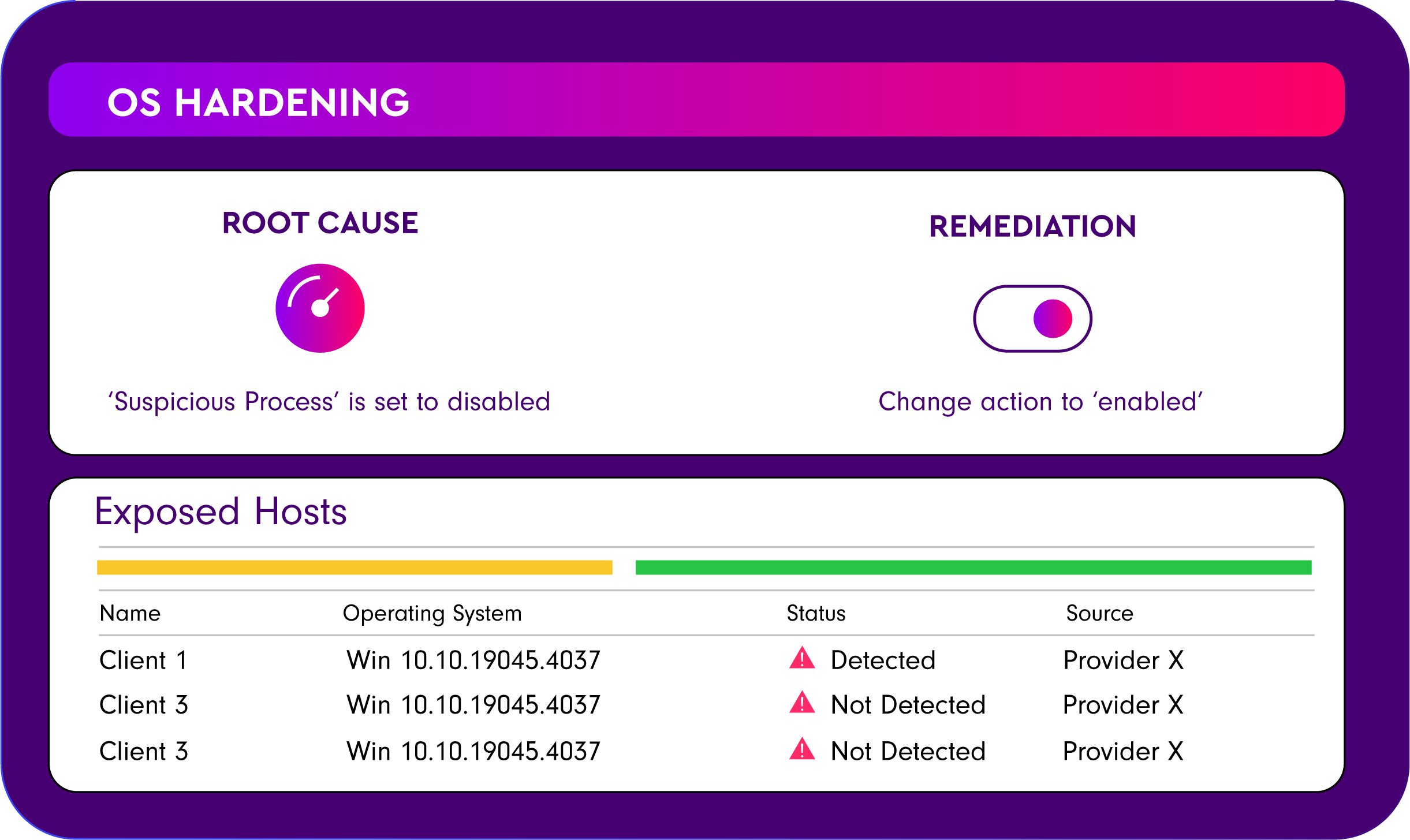
Continuous configuration monitoring
Stay ahead of potential threats by continuously monitoring the hygiene of your security solutions..
Automated assessment and remediation
Verified for business continuity
features
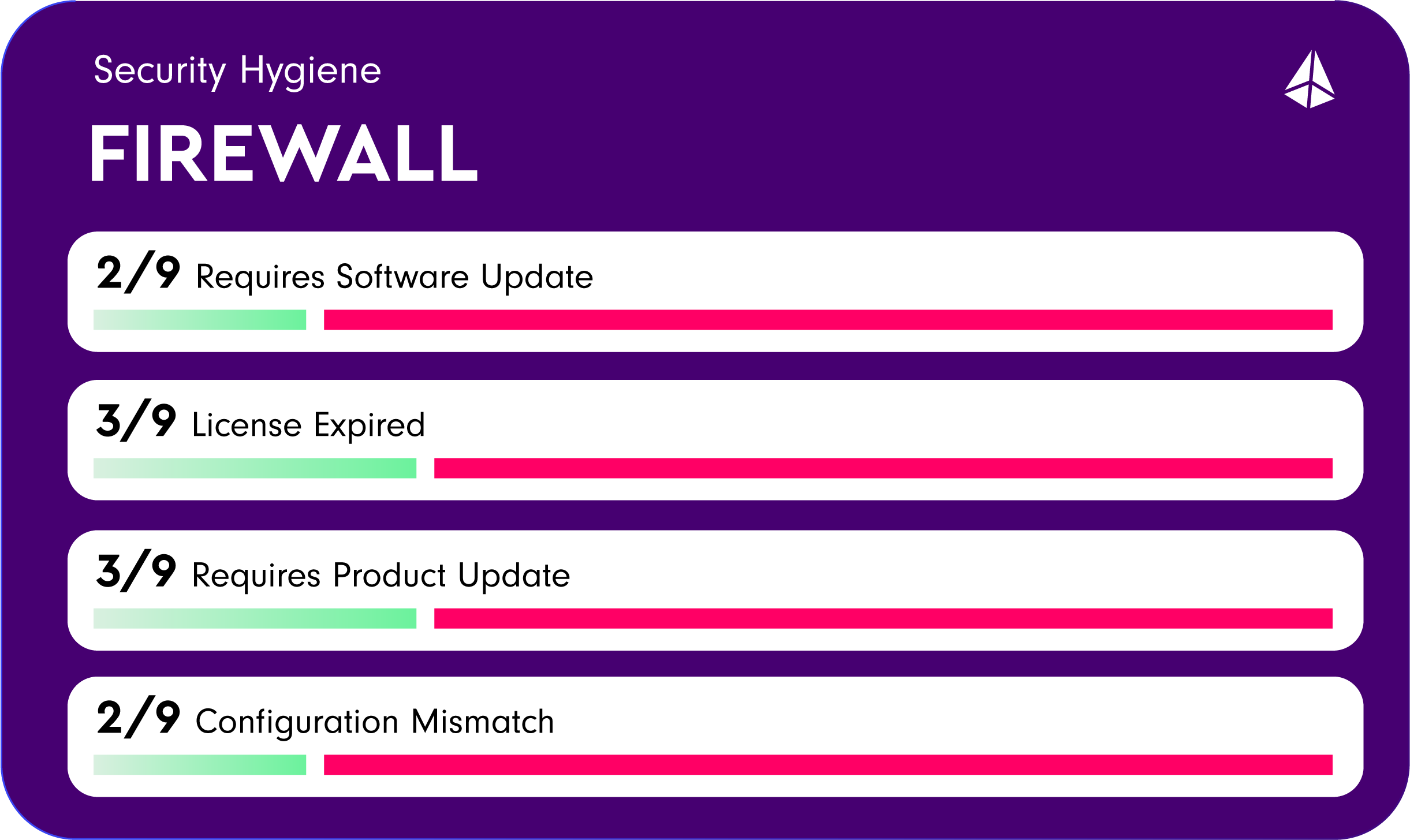
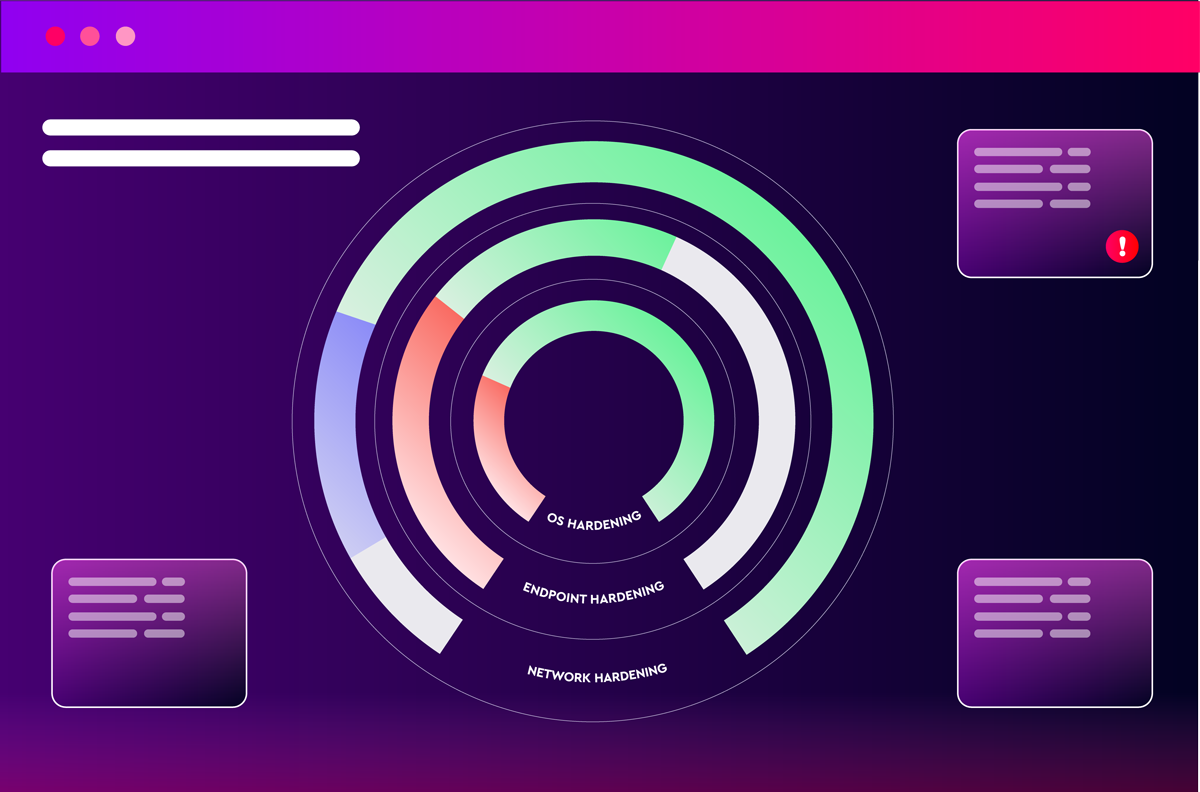
Network hardening
Optimize your network defenses with safe policy adjustments across traditional NGFWs and WAFs. Leverage shared threat intelligence to enhance protection, while addressing issues such as software updates, expired licenses, and configuration mismatches. Keep your network secure and resilient with continuous policy optimization.
Endpoint hardening
Strengthen endpoint security by aligning policies with active threats and automating security changes across tools like CrowdStrike Endpoint Security and Check Point Harmony. Ensure seamless policy implementation without business disruptions, identifying and resolving policy gaps and misconfigurations.
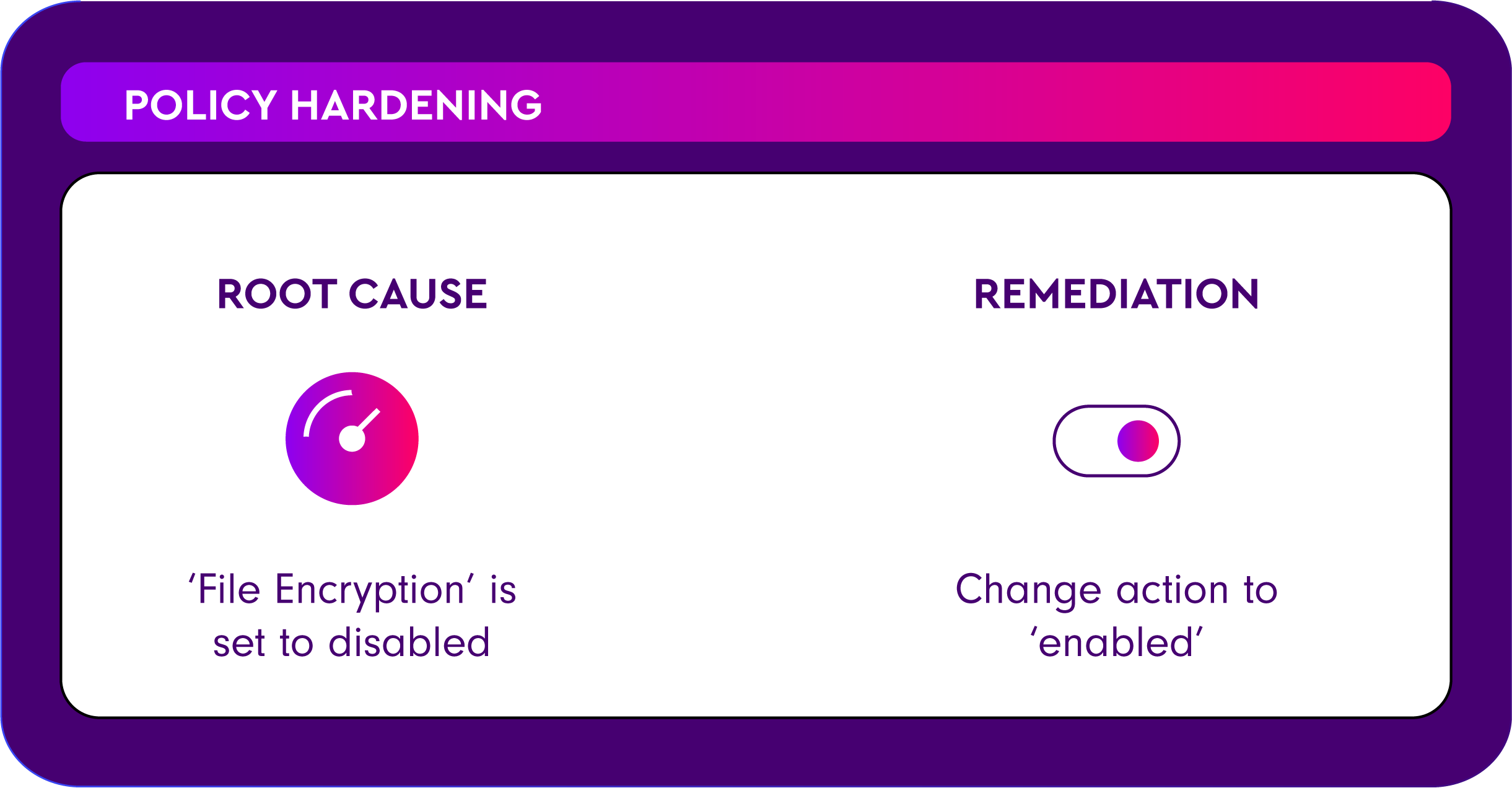
Risk-Based Configuration Adjustments
Utilizing advanced risk assessments and threat intelligence to inform necessary configuration updates, ensuring your defenses remain impervious.
See more use cases
Frequently asked questions
What is Security Control Hardening and why is it important?
Security Control Hardening refers to the regular and consistent maintenance of an organization’s cybersecurity defenses. This includes activities such as software updates, patching vulnerabilities, and monitoring for suspicious activity. It is important because it helps prevent cyber attacks and data breaches by keeping systems and networks up to date and secure.
How often should Security Control Hardening practices be performed?
Security Control Hardening practices should be performed on a regular basis, ideally on a daily or weekly basis. This includes activities such as checking for software updates, patching vulnerabilities, and monitoring for suspicious activity.
What are some examples of Security Control Hardening practices?
Examples of Security Control Hardening practices include:
Keeping software and operating systems up to date with the latest patches and security updates
Regularly running antivirus and malware scans
Securing network connections with strong passwords and two-factor authentication
Regularly reviewing and monitoring system and network logs for suspicious activity
Educating employees on safe browsing and email practices to prevent phishing attacks
How can an organization ensure that Security Control Hardening practices are being followed?
An organization can ensure that Security Control Hardening is being followed by implementing a comprehensive cybersecurity program that includes regular training and education for employees, regular monitoring and testing of systems and networks, and implementing security policies and procedures that are regularly reviewed and updated.
What are the consequences of neglecting cyber hygiene?
Neglecting cyber hygiene can lead to a variety of serious consequences, such as data breaches, financial loss, damage to the organization’s reputation, and legal liability. It can also lead to system downtime, which can negatively impact an organization’s operations and productivity. Additionally, organizations that neglect cyber hygiene may be more susceptible to cyber attacks and may find it more difficult to recover from a security incident.

