Definition: Automated Remediation refers to the process of automatically resolving security issues, system failures, or operational problems in an IT environment. This technology is a key component of modern IT management, enabling organizations to rapidly address issues with minimal human intervention, thereby enhancing efficiency and reducing downtime.
Why Automated Remediation Matters Today
Modern hybrid environments spanning on-prem, cloud, and third-party platforms generate thousands of security alerts daily, many caused by misconfigurations, unpatched vulnerabilities, or disconnected security tools. Manual remediation is no longer scalable, and teams are left overwhelmed, struggling to prioritize and hesitant to act due to fear of disrupting critical operations.
Veriti’s automated remediation process eliminates this operational friction by automatically correlating exposures to their root causes, validating compensating controls, and ensuring every remediation action is both safe and business aligned. This proactive, context-aware approach reduces noise, accelerates response times, and strengthens overall security posture, all without manual intervention.
Key Features and Benefits:
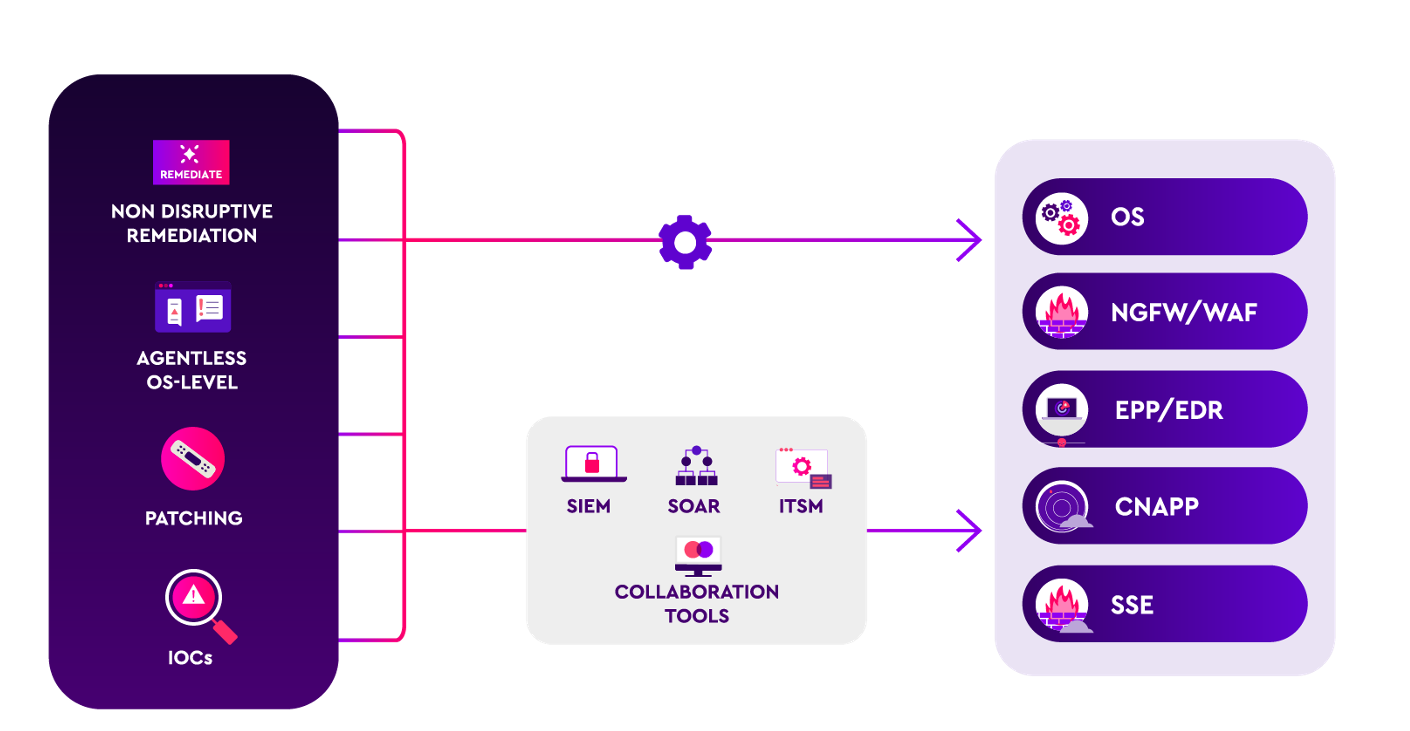
- Direct configuration changes across cloud, endpoint, and network security platforms.
- Automated actions via SIEM, SOAR, and ITSM integrations for seamless remediation workflows.
- Noise reduction through advanced deduplication and correlation across all security tools.
- Real-time correlation between exposures, misconfigurations, and root causes.
- Cross-platform correlation of vulnerabilities with compensating controls.
- Integrated remediation engine for on-prem, hybrid, and cloud environments.
- Proactive IoC propagation across all security tools to enforce coordinated protections.
- Safe remediation with built-in business impact validation to prevent disruptions.
Veriti goes beyond basic automation to deliver true automated vulnerability remediation by combining data from vulnerability scanners, threat intelligence feeds, and security control configurations. This holistic approach ensures every remediation action is safe, contextually aware, and aligned with business priorities.
By seamlessly integrating with over 70 security tools across cloud, on-prem, and hybrid environments, Veriti delivers automated security remediation that bridges gaps between siloed platforms, from firewalls and EDR to cloud platforms and CNAPPs. This ensures vulnerabilities and misconfigurations are not just detected but fully remediated, leveraging the right compensating controls when patching isn’t feasible.
How it Works:
Automated remediation systems monitor IT environments for predefined conditions or anomalies. Upon detection of an issue, the system triggers a response mechanism, such as restarting a service, applying a patch, or reconfiguring settings, based on established protocols. These responses are often customizable to align with the organization’s policies and operational needs.
With Veriti’s automated investigation and remediation capabilities, every exposure is automatically mapped back to its root cause, regardless if it stems from a misconfiguration, unpatched vulnerability, or a missing security control. This ensures teams don’t waste time chasing symptoms and instead focus on resolving the underlying issues with precision.
Veriti’s remediation engine evaluates all available compensating controls, from firewalls to endpoint protection to cloud-native security features, ensuring that automated vulnerability remediation tools apply the safest, most effective action, whether that’s adjusting a firewall rule, propagating an IoC, or recommending a configuration change through ITSM workflows.
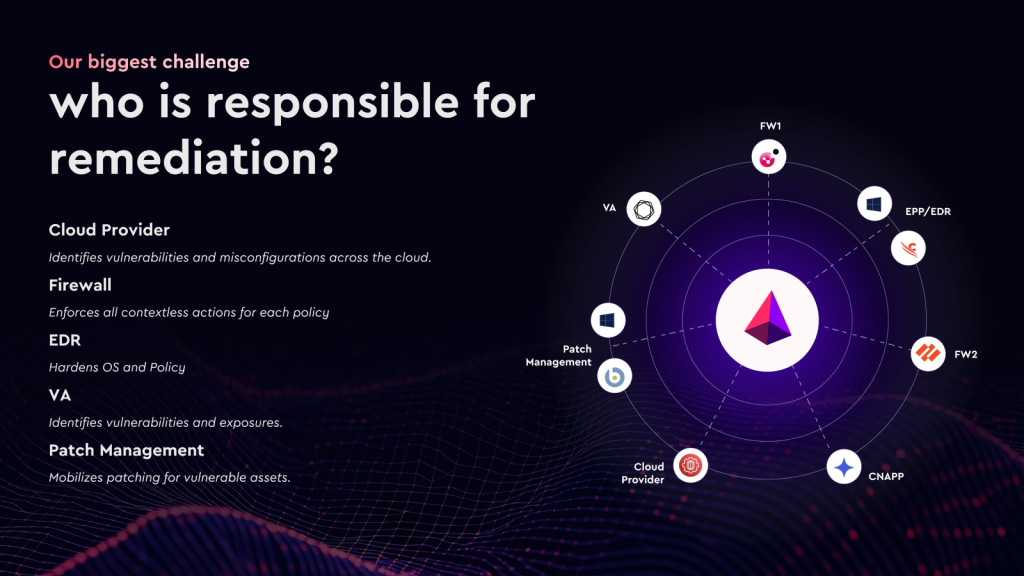
Who Owns Remediation?
One of the biggest challenges organizations face today isn’t just identifying exposures, it’s determining who is responsible for fixing them.
Cloud providers detect misconfigurations. Vulnerability scanners surface exposures. Firewalls, EDR, patch management platforms, and CNAPPs all play a role in applying protections, but none of them work together to coordinate and validate a single, safe remediation plan.
This fragmented reality leads to missed exposures, inconsistent enforcement, and delayed response times, all increasing the risk of breaches. Veriti’s automated investigation and remediation capabilities break down these silos, unifying all security controls into a single remediation engine that applies safe, contextual, and coordinated actions across your entire security stack, from cloud to endpoint.
Use Cases:
- AGENTLESS OS-LEVEL REMEDIATION – Proactively safeguard your systems directly at the OS-Level on the endpoint
- VULNERABILITY REMEDIATION – Safely remediate vulnerabilities in one click
- SECURITY CONTROL HARDENING – Proactively neutralize miscon
- figurations to minimize exposure risks
- INTELLIGENCE ENFORECMENT – Identify and mobilize threat remediation across the security stack automatically
Real Remediation, Not Just Patching
True automated security remediation goes far beyond basic patching. Veriti maps exposures to their root cause, whether a vulnerability, misconfiguration, or missing control, and applies the safest possible action.
If patching isn’t feasible due to operational constraints or legacy systems, Veriti identifies and applies the right compensating controls, from tightening firewall rules to applying advanced threat intelligence based protections.
Every remediation action is validated for business impact before deployment, ensuring no downtime, operational disruption, or broken workflows. With Veriti, security teams gain the confidence to remediate faster, safer, and smarter.
Automated Remediation is an essential tool for modern IT management, offering significant advantages in terms of response time, consistency, cost efficiency, and security. While it greatly enhances an organization’s ability to maintain optimal operational conditions, it requires careful setup and oversight to ensure its effectiveness and alignment with the organization’s specific needs and objectives.




