PROACTIVE EXPOSURE MANAGEMENT WITH SAFE REMEDIATION ACROSS THE ENTERPRISE
Analyze, prioritize, and remediate active vulnerabilities across your organization with the combined power of CrowdStrike’s Exposure Management and Veriti’s Exposure Assessment and Remediation.
EXECUTIVE SUMMARY
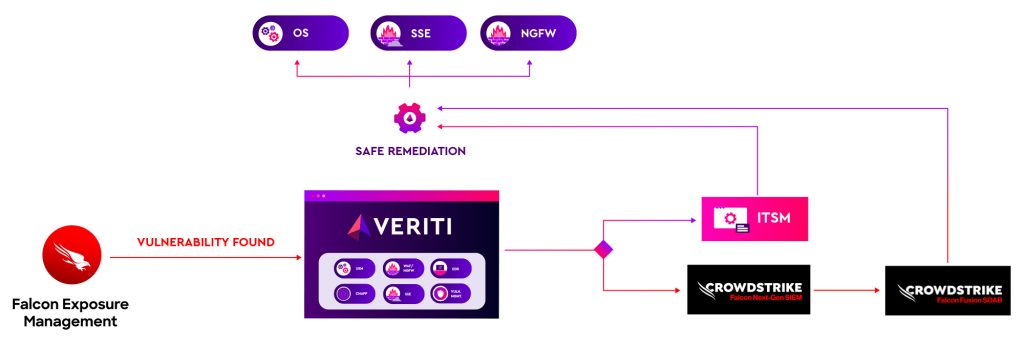
The integration of CrowdStrike’s Exposure Management with Veriti’s Exposure Assessment and Remediation delivers a comprehensive solution for managing and mitigating vulnerabilities across your entire security stack. This powerful partnership provides a continuous analysis of all active vulnerabilities within your organization, prioritizing them based on the availability of your compensating controls. With Veriti’s advanced automation capabilities, the most critical vulnerabilities can be remediated swiftly and safely by directly mobilizing relevant security controls, all while ensuring business continuity.
EXPOSURE MANAGEMENT AND AUTOMATED REMEDIATION
CrowdStrike’s Exposure Management and Veriti’s Exposure Assessment and Remediation work in tandem to provide a proactive and efficient vulnerability management solution. By conducting continuous analysis, this integration identifies all active vulnerabilities within your organization, ensuring no risk goes unnoticed. The solution then prioritizes these vulnerabilities based on the availability of compensating controls, focusing on those that pose the most significant risk and can be effectively mitigated immediately.
Veriti’s exposure remediation capabilities allow for safe and direct remediation by mobilizing the relevant security controls, ensuring that vulnerabilities are addressed without disrupting business operations.
SOLUTION BENEFITS
Comprehensive Risk Visibility: Gain full visibility into all active vulnerabilities across your organization with automated root cause analysis, ensuring that no risk is overlooked.
Efficient Vulnerability Management: Prioritize and address the most critical vulnerabilities based on compensating controls availability, allowing for targeted and effective remediation.
Streamlined Remediation Process: Reduce the time and complexity of vulnerability remediation by directly mobilizing security controls, ensuring that threats are mitigated swiftly and safely.
Maintained Business Continuity: Ensure that vulnerability remediation efforts do not disrupt business operations, maintaining a stable and secure environment while addressing security gaps.
Key Features
Continuous Exposure Analysis
Prioritization by Available Compensating Controls
Safe and Direct Remediation




