TL;DR
Introduction
Recent investigations have unveiled a coordinated attack that integrates two notorious malware types, Agent Tesla and Taskun. Each one is known for their disruptive capabilities, but their combined use marks a new level of sophistication. This analysis dissects the multifaceted approach used by adversaries, leveraging seemingly benign communication methods to deploy highly destructive payloads. Understanding these tactics provides invaluable insights into enhancing our defensive strategies and underscores the necessity for continual vigilance and adaptive security measures.
Agent Tesla and Taskun Malware Insight:
- Agent Tesla – A sophisticated spyware known for its keylogging and comprehensive information stealing capabilities. It systematically captures a variety of sensitive data, which includes keystrokes, screenshots, and various application credentials.
- Taskun – Acts as a facilitator for Agent Tesla, setting the stage for its deployment by first compromising system integrity. Taskun’s role is crucial in maintaining persistence and evading detection, allowing for a deeper entrenchment of the primary payload.
Combined Strategy and Execution
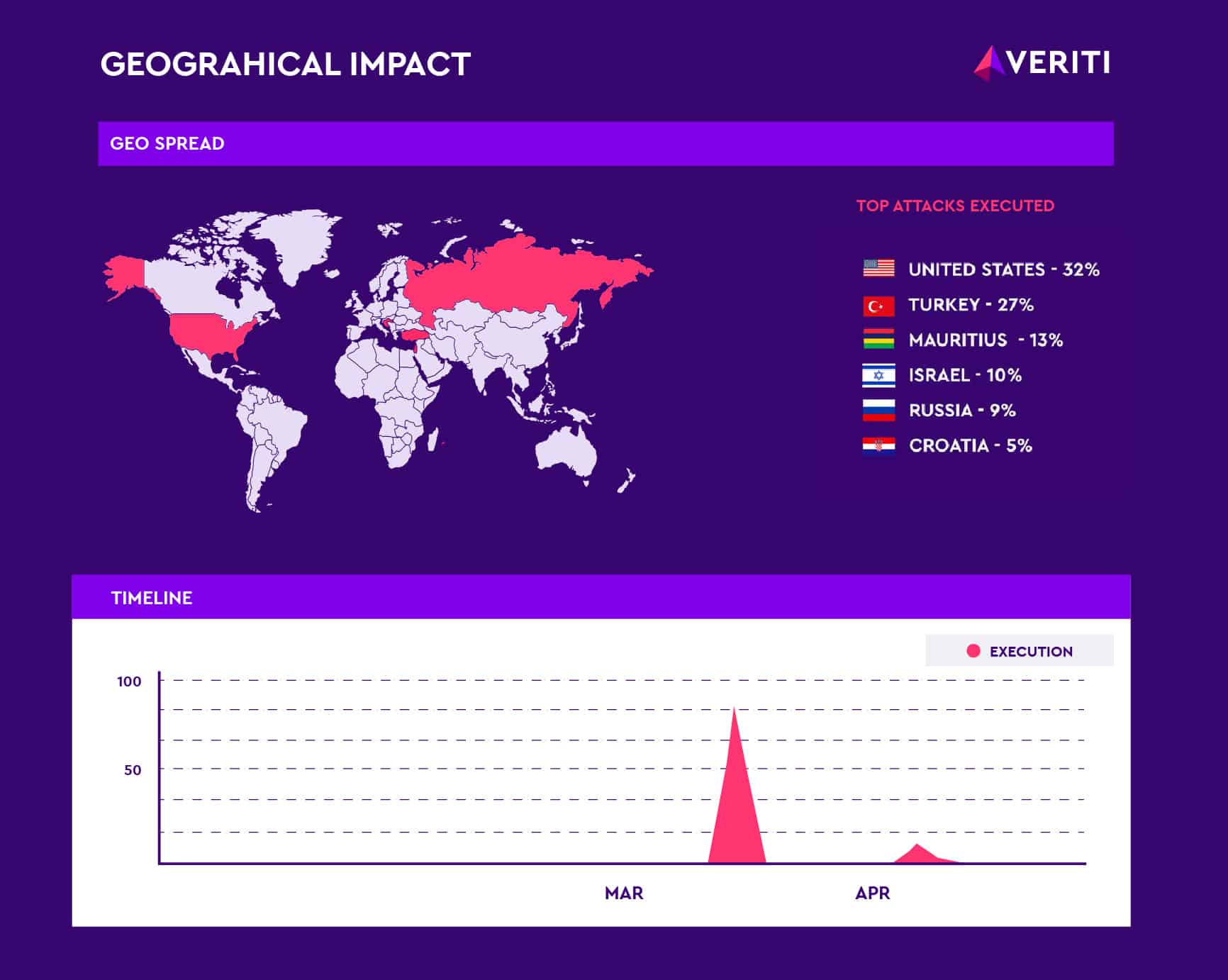
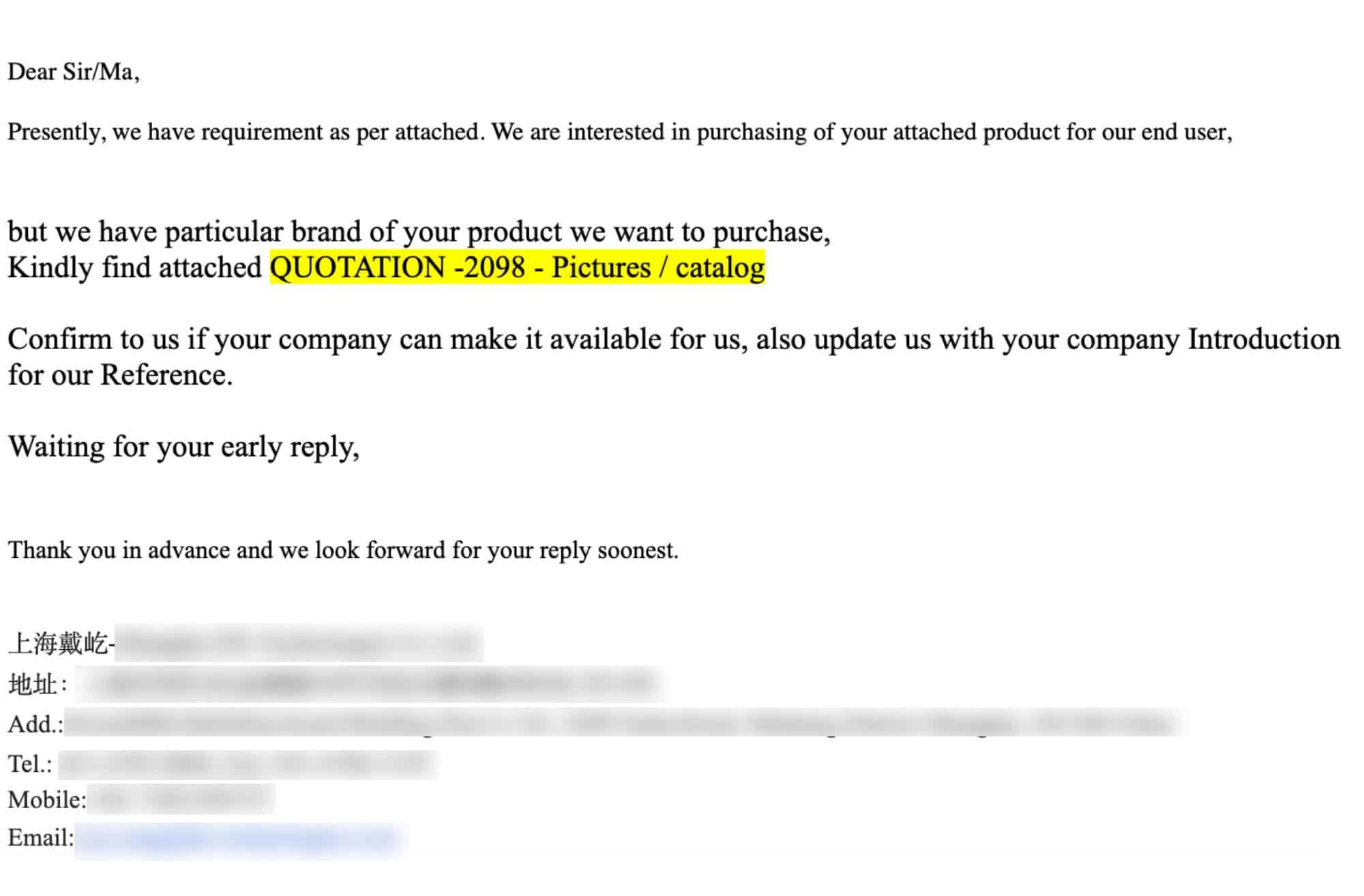
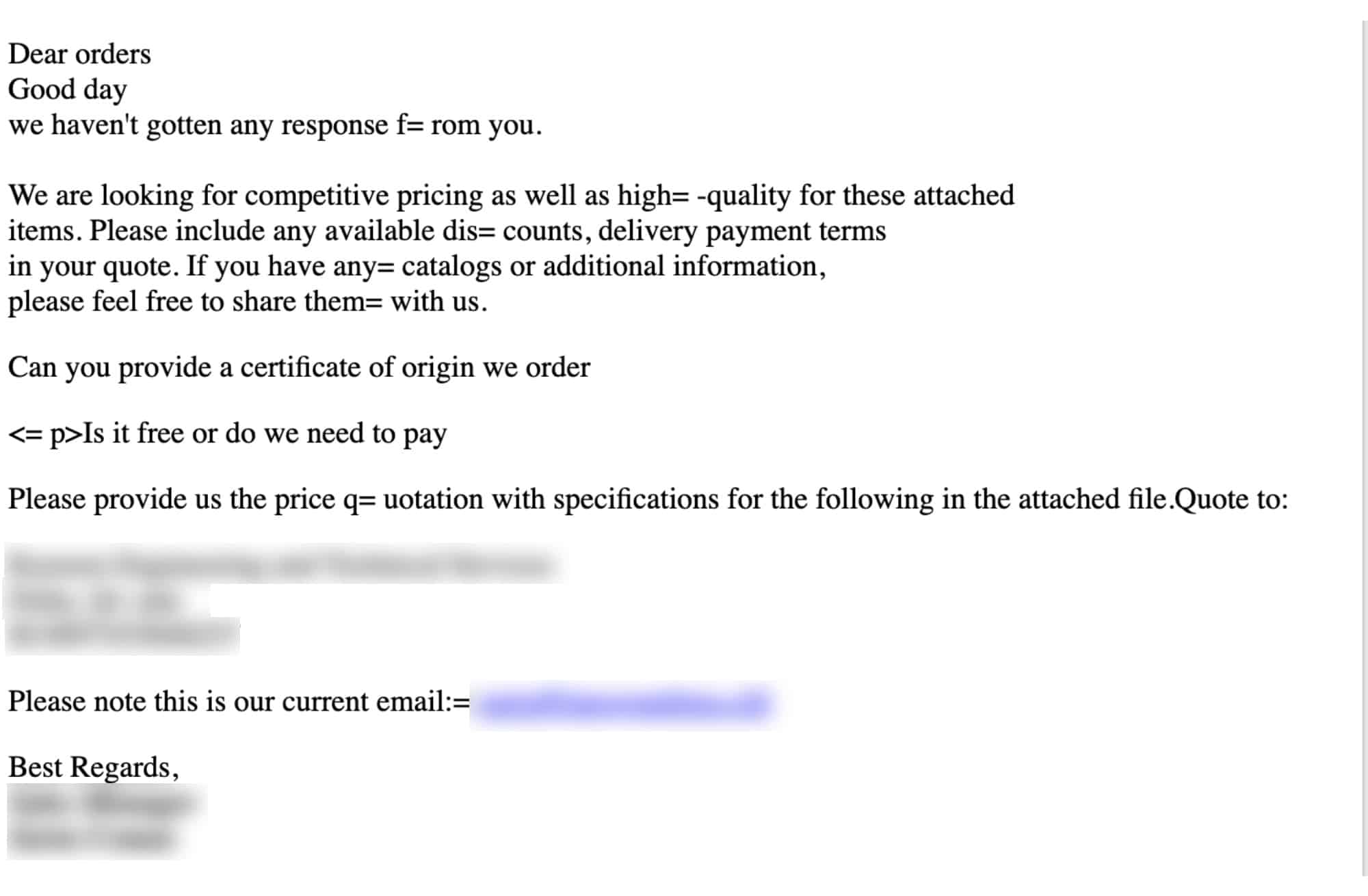
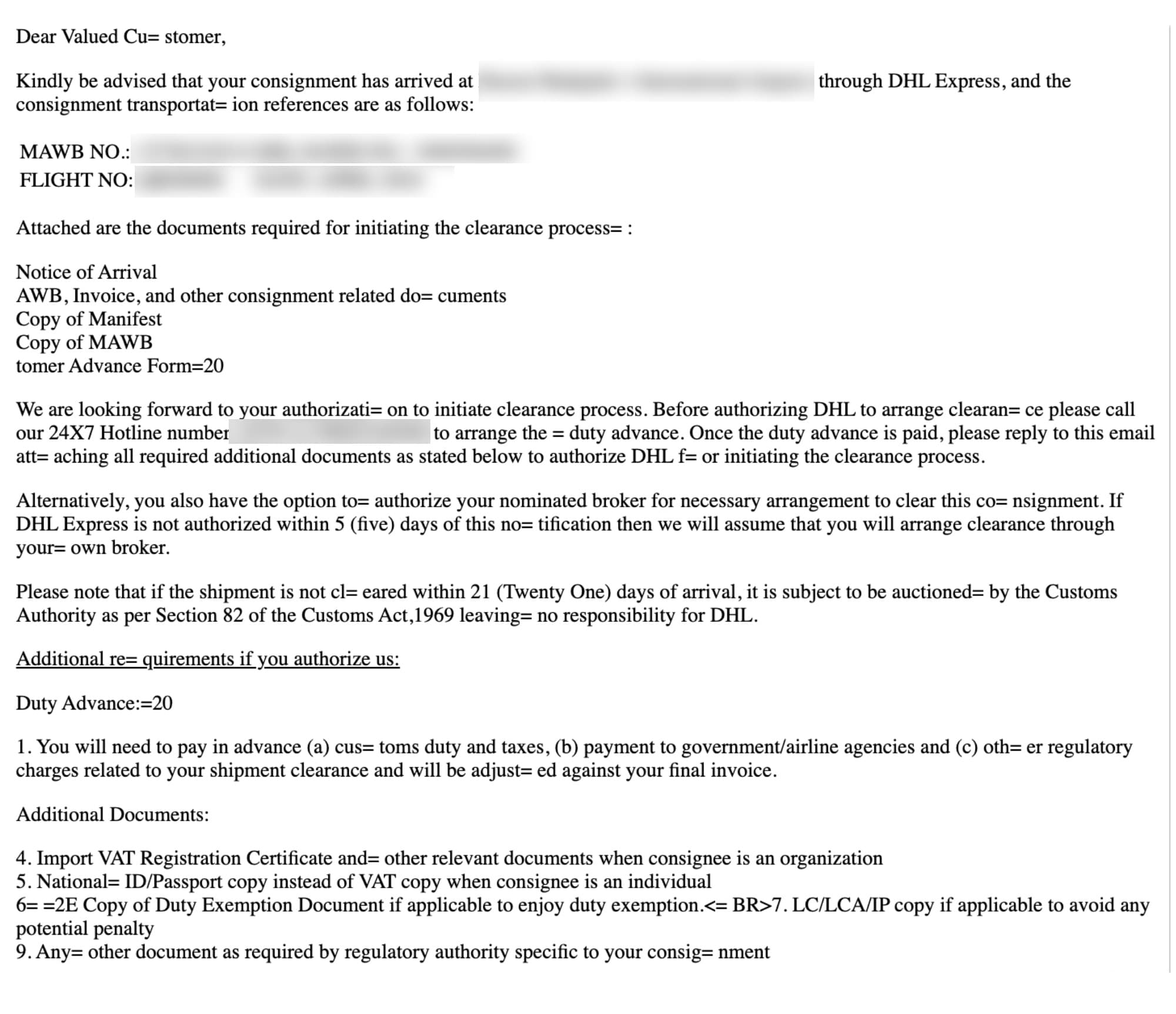
The attack vector utilized in this campaign was primarily through malicious email attachments. It was designed to exploit a series of vulnerabilities across a range of common office and operating system software. The meticulous selection of vulnerabilities indicates a thorough reconnaissance phase, ensuring maximum impact upon execution.
What’s the Risk to Organizations?
The risk to organizations from the coordinated use of Agent Tesla and Taskun malware is considerable, primarily because these threats exploit a range of vulnerabilities across different systems and applications. The technical sophistication and evolving nature of these malware types demand a proactive and comprehensive approach to cybersecurity.
Affected Products
The following table outlines the products affected by the CVEs targeted in this malware campaign:
| CVE ID | Affected Product | Impact |
| CVE-2018-0802 | Microsoft Office | Remote code execution via crafted documents |
| CVE-2017-0199 | RTF for Microsoft Office | Remote code execution via crafted files |
| CVE-2004-0566 | Windows 2000 | Buffer overflow vulnerabilities |
| CVE-2010-2561 | Microsoft Windows | Elevation of privilege |
| CVE-2017-8570 | Microsoft Office | Remote code execution via crafted documents |
| CVE-2018-0798 | Microsoft Office | Remote code execution via crafted files |
Actions Security Teams Should Take:
Pre-Infection:
Targeted Patch Management and Environment Hardening –
Ensure that all systems running the affected software are updated to the latest versions that have patched these vulnerabilities. Alternately identify the relevant compensating controls and technologies and involve them to proactively harden the defenses without waiting for maintenance windows.
Automated Rule Deployment Across Security Controls:
Implement or enhance detection capabilities to monitor for signs of the IOCs related to Agent Tesla and Taskun. Utilize automated rule deployment across security tools, like SNORT and YARA, to detect and block attack attempts.
Endpoint and Network Protection:
Strengthen endpoint defenses to thwart credential harvesting and MITM attacks. This includes disabling legacy protocols like WDigest and securing authentication mechanisms.
Veriti’s OS & GPO Protection:
To combat the tactics used for credential harvesting and MITM (man-in-the-middle attacks), Veriti deploys advanced endpoint protection strategies:
Credential Harvesting Protection:
Direct integration of protective measures into the operating system effectively neutralizes threats from tools like Mimikatz before they can compromise credentials.
Mitigating Man-In-The-Middle (MITM) Attacks:
Vulnerabilities associated with NTLMv2 are addressed by tightening network access controls and enhancing authentication mechanisms, which prevent attackers from intercepting or manipulating data in transit.
Disabling Initial Infection Vectors:
Tools such as the Equation Editor, which have been exploited in various malware campaigns, are disabled via Group Policy settings, cutting off a favorite entry point for attackers and preventing the initial payload delivery.
Command and Control & Exfiltration
To effectively disrupt the communication channels used by Agent Tesla and Taskun, organizations need to ensure comprehensive deployment of IoCs and IoAs across all security layers. The following is a list of IoCs associated with this campaign. It should be distributed and continuously updated across the security infrastructure:
AgentTesla IoCs:
- 1991450173740bcf6b16c3215619f853
- 4f38ee61eff03a89b68ba9f5d58a780e
- 6c673c2a92078d43253daffa0a5a5553
- d63c98b5baa2acced31706b76b8c8180
- ffbb6c54c5d852c2d437d7860235db52
- 463a2935c1571e72efa1f3a6fe64c48a
- 5b5660a50e85506a03ce396709a3fa6d
- 7d39a725113ffc4b0c9bf4b93c0b4571
- a17ab294e66d1b0ed7aa37db582fe180
Taskun IoCs:
- 52728ce7df73b61540a0ecdb8fb61fe7
- c73a4f19784e3b30092e169822e617ba
- d5e2b9feb1242e7c913bb0f8b0d4cadf
Conclusion
The dual-threat nature of Agent Tesla and Taskun demands a robust and multi-layered defensive strategy that encompasses not only immediate threat detection and mitigation but also a deep understanding of threat actor tactics and techniques. By dissecting these attacks, organizations can better anticipate future threats and fortify their defenses against a landscape of ever-evolving cyber adversaries. Our analysis emphasizes the importance of a unified approach to security, where continuous learning and adaptation are key to maintaining resilience against such sophisticated threats.




