The security industry has mastered detection. It has even gotten pretty good at prioritization, or so vendors like to claim. But let’s be real: Detection without remediation is just documentation.
Telling security teams, “Here’s a prioritized list of your most critical vulnerabilities” is not enough as prioritization alone doesn’t prevent breaches; remediation does. And yet, for years, security vendors have treated remediation as someone else’s problem. They flood security teams with findings, risk scores, and best practices, but when it comes to actually closing security gaps, they step back and say, “Good luck.”
That model is broken, and we are now witnessing a critical shift in cybersecurity strategy.
The Evolution of Exposure Management: Where We Went Wrong
Over the past decade, the security industry has moved through distinct phases in how it handles vulnerabilities and exposures:
The Age of Detection (SIEMs, Threat Intelligence, and the Alert Tsunami)
Security vendors first focused on finding threats, churning out alerts and data logs, and expecting security teams to manually sift through them. SIEMs, threat feeds, and forensic tools gave SOCs a flood of observables: IP addresses, file hashes, OS analysis and behavioral anomalies – but little in the way of actionable response.
The Age of Prioritization (Risk Scoring, Context, and Too Many Dashboards)
Realizing that too many alerts caused fatigue, vendors pivoted to prioritization, building sophisticated scoring models, risk analytics, and context-aware insights. This made security teams more efficient at knowing which vulnerabilities mattered most, but the fundamental challenge remained: even the “most critical” risks still required manual effort to remediate.
The Age of Exposure Management (Bridging Silos, but Still Falling Short)
With the rise of attack surface management (ASM), exposure assessment, and continuous threat monitoring, the industry shifted towards mapping vulnerabilities and misconfigurations across hybrid environments. While this approach improved visibility, it still left security teams responsible for executing remediation.
And that’s where we hit a wall.
The cold reality? All the identification, detection, and prioritization in the world doesn’t matter if remediation is still a slow, manual process.
For years, security was trending toward detect and respond, but we are now seeing a fundamental shift back toward protection.
What’s Driving This Change?
- Attackers Are Moving Faster Than Defenders
When vulnerabilities are weaponized within hours of disclosure, security teams can’t afford to spend weeks or months patching. The only way to keep up is through automated mitigation.
- The Cost of Delayed Remediation Is Too High
Every unpatched vulnerability, every misconfiguration, and every ignored “medium-risk” issue remains an open door for attackers. Security teams need solutions that seal those gaps instantly, not just flag them.
- Security Teams Are Overwhelmed
The cybersecurity skills gap is wider than ever, and security teams can’t keep up with manual patching and configuration changes. The solution? Automated remediation that removes human bottlenecks.
- The pendulum is swinging back. The future of cybersecurity isn’t just about detecting threats. It’s about automatically eliminating the risks before they can be exploited.
Remediation: The Responsibility Security Vendors Can’t Ignore
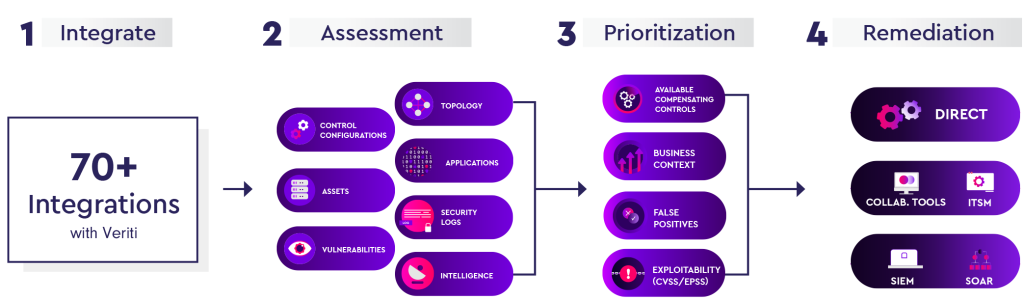
Real automated remediation isn’t just about applying patches or shutting down risky configurations, it’s about understanding the full security context and taking safe, effective action.
- Automated Analysis & Correlation
Every exposure needs to be mapped back to its root cause, whether it’s a misconfiguration, an unpatched vulnerability, or a missing security control. This correlation needs to happen automatically—no manual guesswork.
- Pinpointing Compensating Controls
Sometimes, patching isn’t an option (think legacy systems or operational constraints). In these cases, security platforms must identify and apply compensating controls—whether it’s adjusting firewall rules, applying encryption methods, or distributing IoCs across different security layers for coordinated response.
- Impact Validation Before Applying Changes
Security teams fear remediation because they don’t know what will break. That’s why remediation must include built-in verification mechanisms—simulating changes before deployment to ensure they don’t cause downtime, disrupt workflows, or break integrations.
Without this level of intelligence, remediation just becomes another security headache.
Done right, remediation becomes a seamless, low-friction process that actually makes organizations more secure, without the operational risk.
Auditing: The Backbone of a Sustainable Remediation Lifecycle
Security doesn’t end when an issue is fixed. Every remediation action, whether automated or manual, needs a full audit trail. Why? Because remediation isn’t just about security. It’s about accountability.
- An End-to-End Remediation Ledger
Security teams (and their auditors) need to see every step of the remediation lifecycle—who approved it, what actions were taken, and whether those actions actually reduced risk.
- Audit Logs Need to Be Seamless, Not a Burden
Most security teams struggle with auditing because traditional logging systems are fragmented, inconsistent, and hard to manage. Security vendors must provide a clear, centralized audit log that documents every fix, every update, and every policy adjustment.
- Automated Reporting for Continuous Improvement
Security teams shouldn’t have to manually piece together the effectiveness of their remediation efforts. Vendors need to provide automated insights into what’s working, what’s not, and where remediation processes can be optimized.
Without real-time, transparent auditing, remediation becomes a black hole.
With proper auditing, organizations gain full control over their security posture, backed by clear, provable actions.
Eliminating False Positives: Fix What Matters, Ignore the Noise
Security teams don’t just fear remediation breaking things—they also fear wasting time on false positives. And they should.
False Positives Create Security Debt
Every unnecessary remediation wastes resources, disrupts business operations and reduces confidence in security processes. That’s why remediation must come with automated validation.
Self-Correcting Security: Remediate Without Breaking Business
Security vendors must build continuous feedback loops that ensure remediation actions don’t block legitimate traffic, interfere with normal operations, or disrupt user productivity.
Behavioral Baselines & Adaptive Response
Instead of applying rigid, one-size-fits-all rules, remediation engines must learn from real-world behavior, adjusting dynamically to avoid false positives while still eliminating real threats.
If remediation isn’t smart enough to differentiate between a real risk and a normal business process, it’s not a solution—it’s just another problem.
The Future: Security Vendors Must Own the Fix, Not Just the Alert
The security industry is at a turning point. We’ve spent years refining detection, prioritization, and visibility—but without action, none of it truly reduces risk. The future isn’t about more dashboards, more context, or more insights. It’s about remediation at machine speed- fixing exposures before they can be exploited. Security vendors must step up and take ownership of remediation. No more pushing the responsibility onto security teams. Automation must bridge the gap between detection and real-time mitigation, security teams shouldn’t be left manually implementing compensating controls, or struggling to validate fixes. The industry must return to real protection. The pendulum is swinging back – away from endless alerts and back toward actual security enforcement.
This is the next evolution of cybersecurity: proactive, autonomous, and outcome driven. Vendors that embrace this shift will define the future. The rest will keep selling alerts – while attackers keep winning.




