Amazon GuardDuty is often referred to as the security hub of Amazon’s cloud ecosystem. It provides advanced threat detection by analyzing run-time (OS-level) activities, network traffic logs, and security events. Amazon describes it as “a single runtime monitoring solution for your compute on AWS.”
In our latest Veriti research, we analyzed Amazon GuardDuty logs to uncover emerging threats, attack methods, and security trends in cloud environments.
The Evolution of Amazon GuardDuty
GuardDuty has continuously evolved to include new data types, making it an increasingly powerful cloud security tool. Its threat detection capabilities span across various attack stages, including:
- Reconnaissance: Detects malicious reconnaissance activities like SSH brute force attacks and suspicious login attempts.
- Execution: Identifies and flags malicious file executions.
- Privilege Escalation: Detects unauthorized privilege elevation attempts.
- Defense Evasion: Identifies advanced tactics like fileless execution and memory injection.
- Exfiltration: Detects command-and-control (C&C) communication.

Amazon GuardDuty enables organizations to monitor and protect cloud assets efficiently. Below are some key attack categories GuardDuty detects.
Amazon GuardDuty Detection Categories
GuardDuty’s logs provide valuable security intelligence across multiple categories. Our research mapped GuardDuty’s detection capabilities across different attack scenarios:
| Category | Example Finding |
| Malware Infection | Backdoor C&C Activity |
| Execution | Malicious File Execution |
| Privilege Escalation | Container Mount Host Directory |
| Defense Evasion | Fileless Execution, Anti-Debugging |
| Exfiltration | C&C Communication Detection |
| Unauthorized Access | SSH Brute Force, Metadata DNS Rebind |
| Crypto Mining | CryptoMiner Execution, Bitcoin Tool |
| Remote Code Execution | Reverse Shell, Suspicious Command |
More examples not only from Runtime:
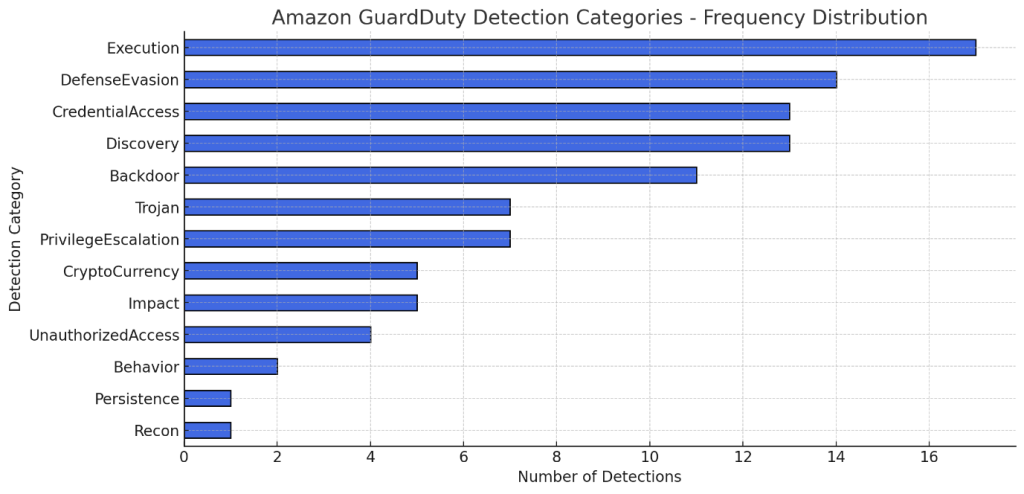
Additionally, GuardDuty offers specific detection capabilities across Kubernetes, RDS, IAM, S3, and other Amazon services. These insights are crucial for security teams monitoring cloud environments.
Use Cases: Real-World Threats and the Role of Amazon GuardDuty
1. Detecting Malware in AWS S3 bucket
Attackers commonly attempt to execute malicious code within cloud environments to establish persistence. One such attack vector involves uploading malware to an S3 bucket.
Amazon GuardDuty scans files uploaded to S3, leveraging both threat intelligence and behavioral analysis to detect malicious activity. Once a threat is identified, Veriti enriches the alerts with related indicators and actively enforces protection against malware, command-and-control (C&C) servers, and malicious IP addresses.
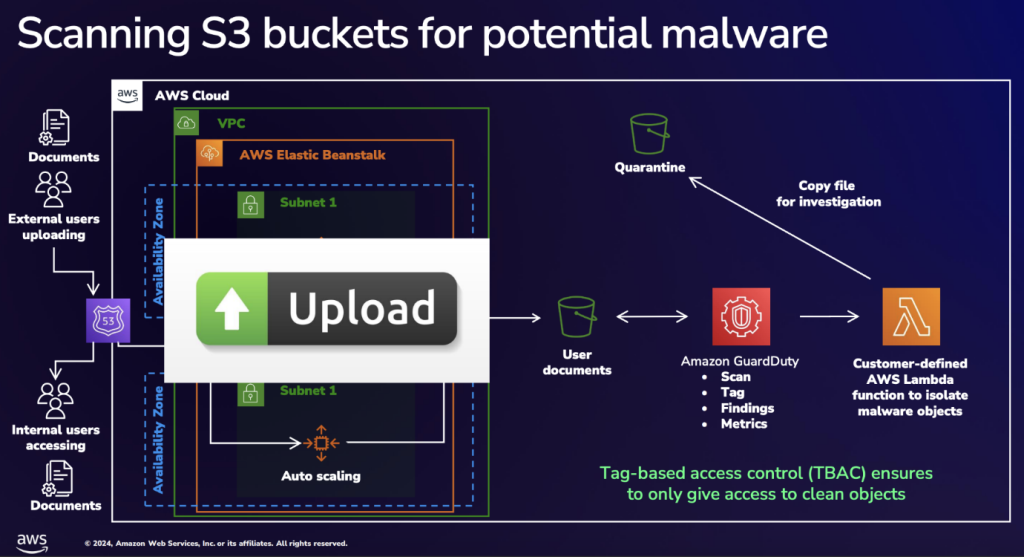
Key takeaway: GuardDuty plays a crucial role in preventing malware from spreading across cloud environments. However, isolation can be challenging in customer-exposed services. Veriti integrates with cloud and on-prem security controls to automate and enforce threat mitigation, reducing exfiltration risks.
2. The Real Story of Cloud Attacks: Veriti’s Research
Over the past few months, the Veriti research team analyzed and automated remediation processes for cloud-based attacks and related IoCs. Here’s what we found:
Top Targeted Industries in the Cloud:
- UK Healthcare
- US Government
- India Utilities
- Bulgarian Government
Top Attack Methods Observed in the Wild:
- RDP Brute Force Attacks
- MySQL Exploits
- SSH Brute Force Attacks
- Exploits targeting known vulnerabilities like:
- CVE-2019-11248
- CVE-2023-46604
- CVE-2017-9841
Case Study: A Successful Ransomware Campaign
Our research uncovered a ransomware campaign leveraging Amazon GuardDuty’s detection capabilities. One notable case involved Cerber Ransomware, which used RDP brute-force attacks to gain access to cloud environments.
Key Findings:
- Attackers initiated brute-force RDP attacks to gain unauthorized cloud access.
- Once inside, they deployed Cerber ransomware, encrypting critical assets.
- GuardDuty detected anomalous network traffic originating from 194.165.16./10, linked to the ransomware campaign.
Additional resources:
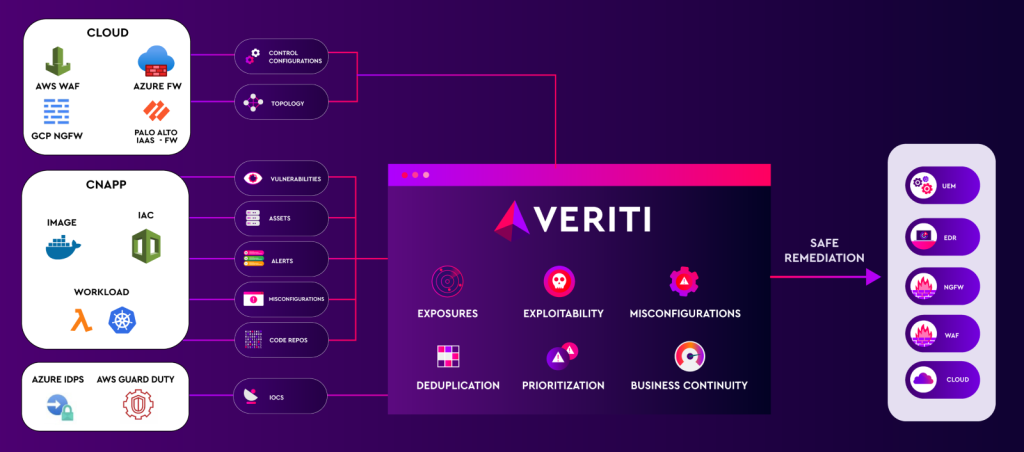
Amazon GuardDuty provides organizations with deep security visibility, identifying a wide range of cyber threats. However, detection alone is not enough, organizations must act quickly to actually remediate risks safely.
At Veriti, we integrate Amazon GuardDuty insights into our exposure assessment and remediation platform, ensuring threats are proactively neutralized across an organization’s entire security estate. By actively enforcing security controls across cloud and on-prem environments, we minimize the impact of attacks and reduce the risk of data exfiltration.
Next Steps
- Review your Amazon GuardDuty configurations to ensure all detection capabilities are enabled and protecting the organization as they should.
- Integrate GuardDuty findings with exposure assessment and remediation solutions to remediate threats faster.
- Learn more about Veriti Cloud to enhance cloud security posture with cloud native remediation and enforcement.




