We all know that vulnerabilities are documented in a centralized list known as Common Vulnerabilities and Exposures (CVE). To gauge the severity of these vulnerabilities, they are assessed using various scoring systems. Among these, the Common Vulnerability Scoring System (CVSS) is widely recognized, currently in its fourth iteration.
However, CVSS has its limitations, primarily focusing on the intrinsic characteristics of the vulnerabilities without considering their likelihood of exploitation. This approach often leads to treating all vulnerabilities with similar scores equally, regardless of their real-world risk implications.
Exploit Prediction Scoring System (EPSS) Overview
Administered by FIRST (Forum of Incident Response and Security Teams), same as CVSS, EPSS estimates the likelihood of a vulnerability being exploited using a model based on actual data of exploitation attempts. This system was introduced at BlackHat 2019, with its framework continuously updated, the latest being in March 2023.
EPSS Methodology
EPSS scores are updated daily and available in CSV format on the FIRST website. Each entry in this data set includes:
- CVE ID: The unique identifier assigned by MITRE.
- EPSS Score: A probability score between 0 and 1, indicating the likelihood of exploitation in the next 30 days.
- Percentile: A value showing how a CVE scores relative to others, with higher percentiles indicating higher risks.
The EPSS model uses machine learning to analyze data from multiple sources, including vulnerability databases and real-world exploitation attempts. It incorporates details such as vendor information, age of the vulnerability, CVSS scores, and more, to predict exploitation likelihood.
Why Consider EPSS?
We previously discussed the limitations of relying solely on CVSS for vulnerability management. EPSS addresses this gap by providing an estimation of the actual risk of exploitation, which is crucial for resource allocation. For instance, patching vulnerabilities based solely on high CVSS scores can lead to significant resource wastage, as demonstrated by the small percentage of high-scoring CVEs that are actually exploited.
EPSS isn’t just an enhancement to CVSS; it’s a crucial shift in the way security teams approach vulnerability management. Traditionally, patching has relied on severity scores, but this approach fails to account for the real-world likelihood of exploitation. By considering actual exploitation data, EPSS bridges the gap between theoretical risk and actual threat, enabling teams to act faster and more efficiently.
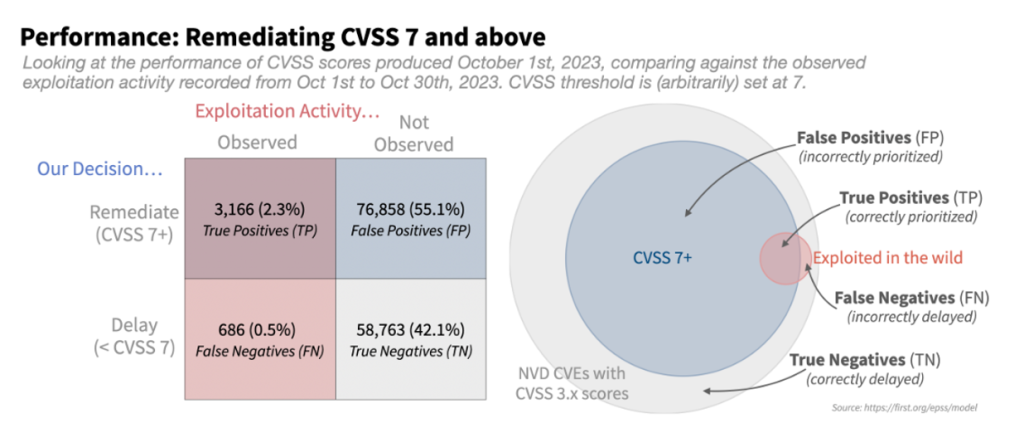
The diagram reveals that a mere 2.3% of the high-severity vulnerabilities (CVSS 7 or above) were exploited (True Positives). Surprisingly, most prioritized vulnerabilities for remediation (CVSS > 7) were not exploited (False Positives), signifying a substantial resource wastage. Addressing this issue is crucial for optimizing resource allocation and enhancing security practices.
For organizations looking to optimize their vulnerability management strategies, EPSS offers an actionable, data-driven approach. Instead of overwhelming security teams with endless lists of high-severity vulnerabilities, many of which may never be exploited, EPSS allows for targeted remediation. This means that teams can focus their efforts on vulnerabilities that pose the greatest risk, without wasting resources on lower-priority issues that are unlikely to be exploited.
Incorporating EPSS for Efficient Remediation
Adopting an EPSS-based approach for vulnerability management allows security teams to focus on the most likely threats, enhancing resource efficiency. For example, focusing on vulnerabilities with an EPSS score of 10% or higher can drastically reduce unnecessary efforts on low-risk issues.
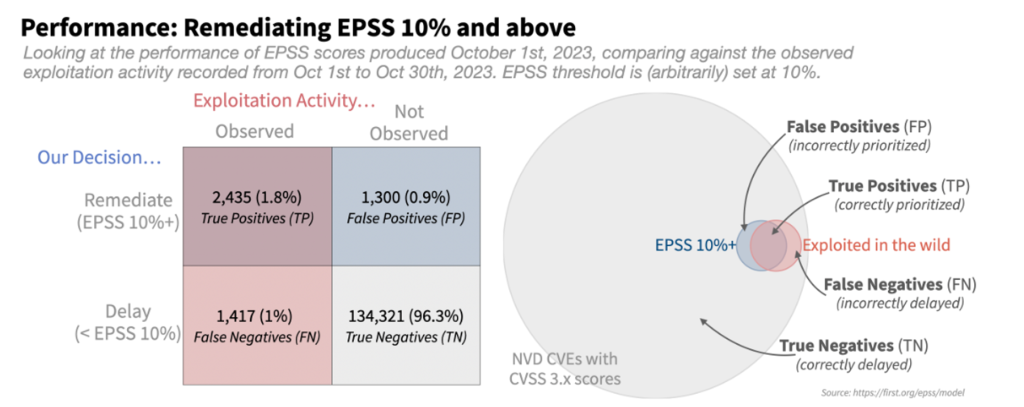
This data reveals that 96% of vulnerabilities with an EPSS score below 10% were not exploited or prioritized for remediation (True Negatives), whereas 1.8% were both exploited and prioritized for remediation (True Positives). This signifies a remarkable decrease in the workload for the security team and a more precise, efficient strategy for handling vulnerability patches. It empowers the remediation teams to concentrate their efforts and resources on the most critical areas within their environment.
Another advantage of using EPSS is its ability to reduce false positives in vulnerability management. With CVSS, it’s easy to fall into the trap of assuming that all high-severity vulnerabilities need immediate remediation. However, EPSS helps differentiate between vulnerabilities that are theoretically severe and those that are actually being exploited in the wild. This refined approach allows security teams to focus on the vulnerabilities that truly matter, improving both resource allocation and overall security outcomes.
While there is some correlation between EPSS and CVSS scores, EPSS provides additional insights, particularly for vulnerabilities that, despite high CVSS scores, have low exploitation probabilities. This nuanced understanding helps prioritize remediation efforts more effectively.
Looking Beyond EPSS and CVSS
While EPSS and CVSS provide valuable insights, they are not definitive. Effective vulnerability management also requires understanding the potential impact on specific systems and the broader network, necessitating a comprehensive assessment of exposure and attack paths.
By integrating EPSS into their vulnerability management workflows, organizations can also improve collaboration between security and IT teams. With clearer priorities and data-backed decisions, both teams can work more efficiently to remediate critical vulnerabilities without getting bogged down in low-risk issues. This level of coordination is essential for reducing the time to remediation and minimizing the risk of exploitation.
Veriti’s platform integrates EPSS to prioritize vulnerabilities effectively, allowing security teams to focus on the most critical issues first. This approach not only saves time but also enhances the overall security posture by addressing the most impactful vulnerabilities promptly.
For more information on how EPSS can refine your security strategies or to see Veriti’s platform in action, schedule a demo with our experts.
Finally, the combination of EPSS and CVSS provides a more holistic approach to vulnerability management. While CVSS gives a useful measure of the technical severity of a vulnerability, EPSS adds an essential layer of real-world context by predicting exploitation likelihood. Together, these tools give organizations a more complete understanding of their risk landscape and enable more strategic decision-making when it comes to patching and remediation efforts.




