The holiday season is a time of joy, celebrations, and—unfortunately—a spike in cybersecurity threats. Cybercriminals often exploit the festive cheer, targeting individuals and organizations distracted by the season’s busyness. This three-part blog series dives into the biggest cybersecurity incidents that occurred around Christmas, their lessons, and what we can learn to protect ourselves during this vulnerable time.
In Part 1, we unwrap the breaches and vulnerabilities from last December, recounting high-profile attacks on food and entertainment industries and other sectors. Stay tuned for Part 2, where we explore the infamous ELF malware and other seasonal threats, followed by Part 3, which will highlight the tools hackers use to exploit holiday gift-giving trends.
AN EVENING WITH FOOD AND MOVIES
The holiday spirit isn’t limited to families gathered around meals and movies; it extends to cybercriminals feasting on vulnerabilities in major industries. Last December, two high-profile breaches captured headlines.
Kraft Heinz: A Cyber Catchup You Didn’t Want
The Snatch extortion group targeted Kraft Heinz, a giant in the global food and beverage industry, creating chaos during the holiday rush. The breach affected operational systems, exposing sensitive data and threatening the company’s reputation. As families stocked up on holiday essentials, this attack highlighted how even resilient organizations can be brought to their knees by sophisticated attackers. More details on the Kraft Heinz breach here.
National Amusements: Not So Amusing Data Breach
National Amusements, which owns and controls numerous popular entertainment brands, also fell victim to cybercriminals. The breach compromised names, financial account numbers, credit card numbers, debit card numbers and PINs of over 82,000 individuals, including financial and card information. The timing couldn’t have been worse—just before Christmas—a stark reminder that entertainment companies are prime targets for data theft during peak consumer activity.
PRESENTS BENEATH THE TREE
The gift-giving season is all about joy, but for cybercriminals, it’s the season of opportunity. Two significant incidents from last December exemplify this.
Ubisoft Breach: Gaming Consoles and Compromised Accounts
Gaming company Ubisoft faced a breach during the holiday shopping frenzy. Hackers accessed usernames, email addresses, and encrypted passwords from its account database. While no financial details were stolen, the incident served as a reminder of the importance of secure account credentials, especially for parents buying games for their children.
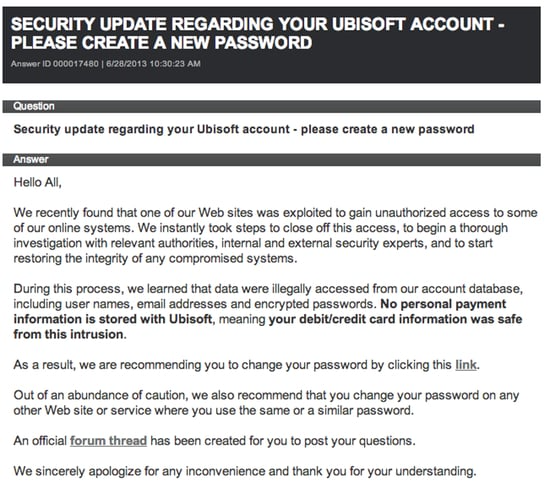
Ubisoft’s security update.
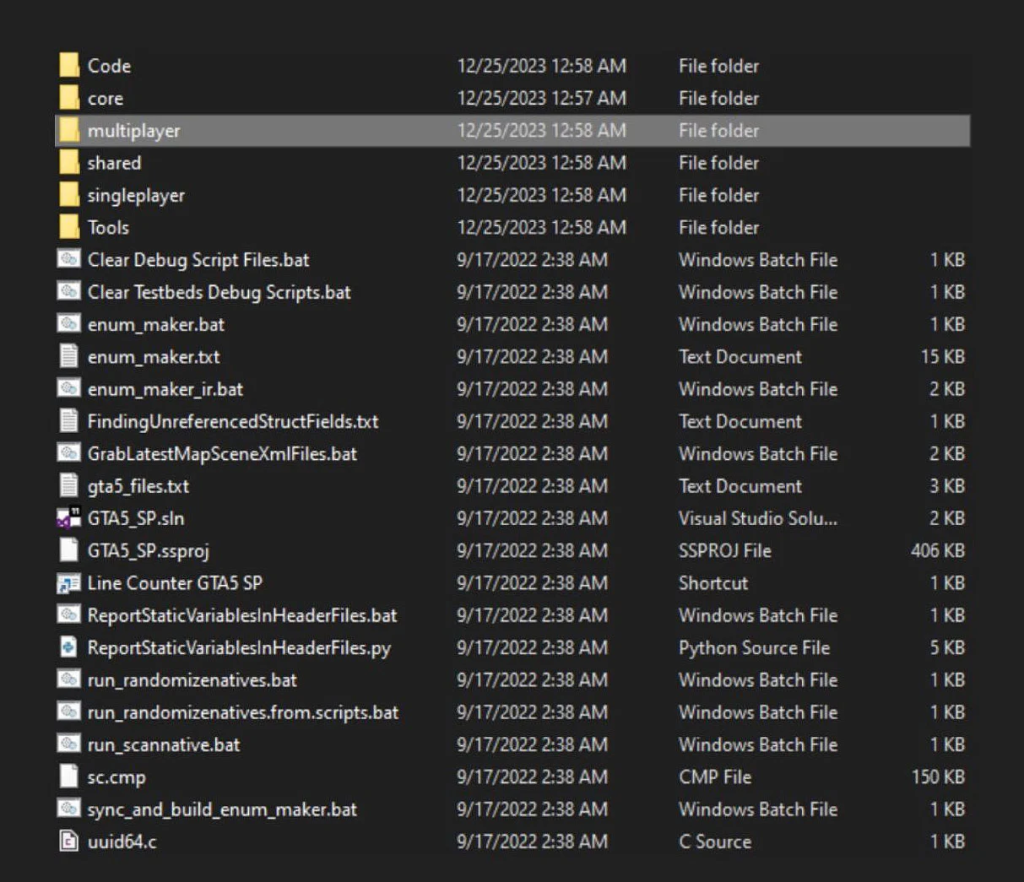
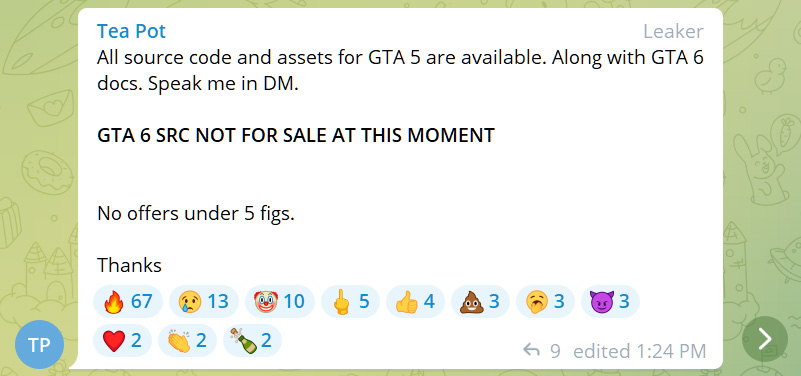
Grand Theft Auto: Lapsus$ Strikes Again
The infamous Lapsus$ hacking group added Rockstar Games to its victim list, leaking source code and assets for Grand Theft Auto 5 and teasing access to GTA 6. This high-profile breach showcased how intellectual property theft impacts the gaming industry, often aligning with periods of heightened consumer interest.
A FLURRY OF VULNERABILITIES
The holiday season also saw a blizzard of software vulnerabilities exploited by hackers across the globe. Let’s look at some of the most notable ones:
| DATE | CVE | DESCRIPTION | IMPACT |
| December 02, 2023 | CVE-2020-0688 CVE-2021-26855 CVE-2021-27065 CVE-2022-41082 CVE-2023-21529 CVE-2023-36745 CVE-2023-36439 | Tens of thousands of Microsoft Exchange email servers in Europe, the U.S., and Asia exposed on the public internet are vulnerable to remote code execution flaws. | Over 20,000 vulnerable Microsoft Exchange servers exposed to attacks |
| December 04, 2023 | CVE-2023-23397 | Microsoft’s Threat Intelligence team issued a warning earlier about the Russian state-sponsored actor APT28 (aka “Fancybear” or “Strontium”) actively exploiting the CVE-2023-23397 Outlook flaw to hijack Microsoft Exchange accounts and steal sensitive information. | Russian hackers exploiting Outlook bug to hijack Exchange accounts |
| December 05, 2023 | CVE-2023-26360 | The U.S. Cybersecurity and Infrastructure Security Agency (CISA) is warning about hackers actively exploiting a critical vulnerability in Adobe ColdFusion identified as CVE-2023-26360 to gain initial access to government servers. | Hackers breach US govt agencies using Adobe ColdFusion exploit |
| December 07, 2023 | CVE-2023-23397 | Russian APT28 military hackers used Microsoft Outlook zero-day exploits to target multiple European NATO member countries, including a NATO Rapid Deployable Corps. | Russian military hackers target NATO fast reaction corps |
| December 10, 2023 | CVE-2021-44228 | Roughly 38% of applications using the Apache Log4j library are using a version vulnerable to security issues, including Log4Shell, a critical vulnerability identified as CVE-2021-44228 that carries the maximum severity rating, despite patches being available for more than two years. | Over 30% of Log4J apps use a vulnerable version of the library |
What’s Next?
As we conclude Part 1, the key takeaway is clear: the holiday season, while joyous, is also a prime time for cyberattacks. In Part 2, we’ll explore how malware like ELF gains traction during the holidays, turning everyday devices into attack vectors. Stay tuned for more insights as we unravel the dark side of Christmas cybersecurity.




